-
Best Australian Pokies Best Payout
Play Free 777 Pokies Online
What Are the Best Australian Pokies to Win Big On
What Are the Best Online Pokies with Low Minimum Deposits for Real Money in Australia
New Australian Pokies Accepting PayID
What Are the Best Strategies to Win in Online Pokies with Bonus Rounds in Australia
Tips for Winning Top Australian Pokies
What Online Casinos Offer Free Play Pokies with Welcome Bonuses in Australia
Australian Slot Games
Payout Ratio Pokies with Welcome Bonus
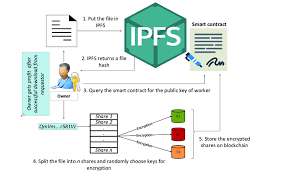
Data Management based on IPFS (Block chain). IPFS is a distributed database with peer-to-peer file system and uses content-addressable hash value which is used to verify the data. Using IPFS, one can upload the data in the form of text, images as well as videos.
Data Management based on IPFS (Block chain)
THESIS PROPOSAL
Research Title: Data Management Based on IPFS (Blockchain)
Introduction
IPFS is a distributed database with peer-to-peer file system and uses content-addressable hash value which is used to verify the data. Using IPFS, one can
upload the data in the form of text, images as well as videos. While uploading the data in IPFS, the protocol returns a unique hash value for the data via
gateway.
This hash value is securely stored in Blockchain. Based on the hash value, the data can be retrieved. In IPFS, data is distributed among the network
participants locally.
Objectives
The proposed scheme combines both IPFS and Blockchain technologies. IPFS is used for storing large volume of data, removes duplication, share files, and
hosts them. The aim of the research minimizes the central server storage space, improves data security by using unique content-addressable hashes for
data verification and also reduces computing power.
Methodology
Proposed Scheme 1 Blockchain issues:
• Storage on the blockchain is so expensive.
• Storing large data and files on the blockchain makes it a dead loss. The blockchain can hardly record a balance transfer for a transaction that includes
small strings of the text, then how is it possible to store large files or images on the blockchain?
How IPFS Solves?
• The storage cost problem on the blockchain can be solved through cryptographic hashes. When hashing a file, for each file (Gupta et al. 2015) and its data,
we can get a fixed length string that is unique. IPFS follows a distinct method, by simply storing the hashes on the blockchain rather than storing the files.
Proposed Scheme 2 • A user who wants to recover any file can access the abstraction layer and just call the hash of the file. It then goes through nodes and
provides the user with the desired file.
• A user who wants to upload a word documents to IPFS, puts his document file in his/her working directory. If he/she wants to add this file, IPFS generates a
hash for this file. Now his/her file is available on the IPFS network.
Data Management based on IPFS (Block chain)
By the development and advancement of blockchain technique, Internet of Things (IoT) proliferation driven devices and the application of blockchain-enabled IoT alter the view and operating infrastructure of the smart networks.
The blockchain is responsible for supporting decentralized systems and offers secured means of authentication, management, and access to IoT system thereby deploying smart contracts offered by Ethereum. The increasing demand and the blockchain expansion generate huge volume of sensitive data.
The growing demand and expansion of blockchain-IoT systems is generating large volume of sensitive data. Furthermore, distributed denial-of-service (DDoS) attacks are regarded as the most promising threats for smart contracts in the blockchain-based systems.
Therefore, there is a need to detect and classify the attack type and the data should be stored in server more securely with the use of blockchain and data aggregation method. For this purpose, this presented technique aims at introducing decentralized consensus blockchain and Interplanetary file system (IPFS) based data aggregation for effective classification and data storage.
The attack is detected using meta-hyperparameter random forest (MHP-RF) classifier.
Once the attack is detected, the transaction information is stored in server securely by means of smart contract-based blockchain system. The transaction handling stage classifies the transaction type as normal or abnormal one which then followed by execution of business logic by smart contract thereby appending the transaction of blockchain in the network cloud.
The consensus blockchain technique is employed with the use of PoW-enabled scheme integrated with Elgamal-based data aggregation. Therefore, the system security is improved and the intrusion is prevented greatly.
The performance analysis of the system is analyzed in terms of accuracy, precision, recall, F-score, Encryption time, decryption time, execution time, and space complexity. The attained outcomes are compared with traditional approaches to prove the effectiveness of proposed strategy. The proposed system is said to be effective in time consumption, classifier performance, and in overcoming space complexity issues.
Attachments
